
It took a country-wide power outage in Venezuela, whispers of a cyberattack, and smug tweets from US officials to make me suddenly recall the cloak-and-dagger story of a close Iranian-American friend nine years ago.
My friend, an engineer — who I will not name for obvious reasons and who I will call ‘Kourosh’ for the purpose of this article — revealed to me in 2010 that he was approached by two “State Department employees” who offered him $250,000 to “do something very simple” during his upcoming trip to Tehran.
Kourosh was freaking out because he didn’t know how these guys knew he was going to Iran in the first place, and how they knew he was “cash-strapped,” in the second.
He wasn’t a particularly political person, though he had participated in some DC protests in the aftermath of the hotly contested 2009 presidential elections. He was just one of thousands of Iranian-American engineers in the Washington-Maryland-Virginia technology belt looking to make a decent living.
Kourosh told the US officials that he was not interested, that if Iran needed to make changes, Iranians inside the country were the only ones who should do it.
I begged him to let me write this story, but he was very nervous and declined. Over the next year or two, I pushed some more and he gave me further information, but wouldn’t budge on its publication. Here’s what he revealed:
The State Department guys had since approached him a second time. They offered him further details about the job. They wanted him to disable Tehran’s power grid in exchange for the $250k. They needed someone with technical skills, but said the job was a simple one. He would have to go to a specific location in the Tehran area with a laptop or similar communication device and punch in a code.
Kourosh even told me the code. Said he had memorized it and could recite it in his sleep. Here it is: 32-B6-B10–40-E (symbol for epsilon)
Okay, that’s not the actual code, but it looks exactly like that — same format, same sequence and amount of numbers and letters. I don’t feel comfortable publishing the code in case it is still relevant — sorry.
If anyone knows what this code could be, please comment below. A colleague with an engineering background has this to say about it: “This could be a password for power grids or any equipment that is governed by an electronic or computer system. Manufacturers have codes they use for de-bugging or resetting a system. Control systems are all electronic and sometimes for any reason (like an earthquake) something is triggered and the system goes off. And then you reset it within the vicinity of the system usually and feed in the new code. You don’t have to physically be there if you can hack into it, but that’s of course harder. If they (the Americans) needed to have someone physically there during the sabotage attempt, it probably means they didn’t have remote access to the system.”
I don’t actually know why Kourosh received that level of detail unless he was willing to go through with this act of sabotage on behalf of the US government, but he assured me he would never consider it — that he was just “curious” during the second meeting. “No way,” he told me. “Imagine it I did it and someone’s grandmother or father died because their life support machine switched off.”
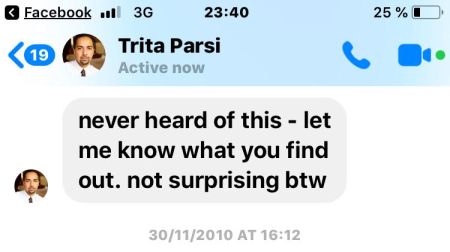
I remember these details because I discussed it with a number of people in and around 2010, without disclosing Kourosh’s name. Today, I dug up the old Facebook message I sent to Iranian-American author and activist Trita Parsi of the DC-based National Iranian-American Council (NIAC), a fellow Huffington Post blogger at the time. Trita gave me permission to post screenshots here:

Disclosure: My Iranian-American husband and I ran an internet company in the telecommunications industry in Washington years ago and I was a founding member of the Iranian-American Technology Council, so I knew a lot of engineers and technology folks from that very background.
I recall writing to Trita precisely because he was so keyed into the political heart of this community. It would be extremely dangerous for myself and colleagues in my industry if the US government was recruiting Iranian-American civilian engineers as saboteurs in third countries.
This deep-dive by investigative journalist Whitney Webb into Venezuela’s power outage reveals some interesting details about a Bush administration cyberattack plan against Iran. Exposed by the New York Times in 2016, the “Nitro Zeus” plan — which involved the US Cyber Command — would, among other things, target crucial parts of Iran’s electricity grid.
Take note, however, that US officials asked Kourosh to sabotage Tehran’s power grid during the Obama administration. Obviously aspects of the Nitro Zeus plan remained on the table despite a switch in government, political parties and policies.
Back to Venezuela
It’s been a grueling week for Venezuelans dealing with the nationwide blackout that has brought the country to a standstill. Last Thursday an “accident” at the Guri Dam power plant in Bolivar state — which generates around 80% of the country’s electricity — left at least 20 out of 23 Venezuelan states without electricity.
As power started to flood back to central states, a second “cyber attack” on Saturday plunged the country back into darkness. Government authorities have charged US officials with launching the attack on Venezuela’s electricity infrastructure and say they will present evidence of this to the United Nations and other international organizations.
The US has countered, blaming the power outage on corruption and infrastructure neglect by the government of President Nicolás Maduro — against whom Washington has been staging a rather unsuccessful coup effort these past months.
But in the midst of this to-and-fro between longtime adversaries, insightful news reports and analysis are starting to emerge, suggesting that a US cyberattack against Venezuela’s power grid is actually a very possible — even likely — scenario. Says Forbes Magazine‘s Kalev Leetaru:
“In the case of Venezuela, the idea of a government like the United States remotely interfering with its power grid is actually quite realistic. Remote cyber operations rarely require a significant ground presence, making them the ideal deniable influence operation.”
“Widespread power and connectivity outages like the one Venezuela experienced last week are also straight from the modern cyber playbook. Cutting power at rush hour, ensuring maximal impact on civilian society and plenty of mediagenic post-apocalyptic imagery, fits squarely into the mold of a traditional influence operation,” he continues.
For those of us who have spent years covering US irregular warfare in the Middle East, infrastructure targets are part and parcel of these wars — sometimes via direct strikes, other times via proxies and sabotage operations.
I’m not just talking about cyberattacks like the US/Israeli-made Stuxnet virus that destroyed hundreds of centrifuges at Iranian nuclear facilities.
In Syria, for instance, the US military specifically targeted major economic infrastructure under the guise of ‘fighting ISIS.’ These include but are not limited to oilfields, wells and facilities, electrical transformer stations, gas plants, bridges, canals, a number of vital dams and reservoirs in the country’s northern agricultural belt — and power generation facilities.
And US-backed proxies — part of the Pentagon and CIA’s ‘irregular army’ in Syria — targeted bread factories, wheat silos and flour mills to deprive a population of basic food staples.
As opposed to conventional wars, US irregular warfare seeks to covertly use influence ops to turn the largest part of a country’s population, the “uncommitted middle,” into supporting regime-change. Destroying infrastructure, creating shortages, unleashing political violence, propaganda dissemination — these are all steps outlined in the US military’s Special Forces Unconventional Warfare manual to create a disgruntled population that will turn on its government.
And cyber warfare is the newest theater of engagement for the Pentagon, which is now openly ramping up its investment in “lethal cyber weapons,” regardless of the civilian casualties these attacks will leave in their wake.
So far in Venezuela around 20 people are reported dead due to the blackouts, though I’ve seen some opposition sources place that number north of 70.
Is Venezuela’s blackout part of US cyber warfare against a Latin American adversary? Has the US engaged in cyber warfare against Iranian infrastructure?
Does a duck quack?
Follow me on Twitter and Facebook if you like. This article was first published on Medium.com on March 14, 2019.
Pingback: Links March 2019 | Mato's Blog